Archive
Single File Restore – Fairy Tale Ending Going Down History Lane – via @Nutanix and @dlink7
Great blog post by Dwayne Lessner!
If I go back to my earliest sysadmin days where I had to restore a file from a network share, I was happy just to get the file back. Where I worked we only had tape and it was crapshoot at the best of times. Luckily, 2007 brought me a SAN to play with.
 The SAN made it easier for sure to go back into time and find that file and pull it back from the clutches of death by using hardware based snapshots. It was no big deal to mount the snapshot to the guest but fighting with the MS iSCSI initiator got pretty painful, partly because I had a complex password for the CHAP authentication, and partly because clean-up and logging out of the iSCSI was problematic. I always had ton of errors, both in the windows guest and in the SAN console which caused more grief than good it seemed.
The SAN made it easier for sure to go back into time and find that file and pull it back from the clutches of death by using hardware based snapshots. It was no big deal to mount the snapshot to the guest but fighting with the MS iSCSI initiator got pretty painful, partly because I had a complex password for the CHAP authentication, and partly because clean-up and logging out of the iSCSI was problematic. I always had ton of errors, both in the windows guest and in the SAN console which caused more grief than good it seemed.
Shortly after the SAN showed up, VMware entered my world. It was great that I didn’t have to mess with MS iSCSI initiators any more but it really just moved my problem to the ESXi host. Now that VMware had the LUN with all my VMs, I had to worry about resignatureing the LUN so it wouldn’t have conflicts with the rest of production VMs. This whole process was short lived because we couldn’t afford all the space the snapshots were taking up. Since we had to use LUNS we had to take snapshots of all the VMs even though there were a handful that really need the extra protection. Before virtualization we were already reserving over 50% of the total LUN space because snapshots were backed by large block sizes and ate through space. Due to the fact that we had to snapshot all of the VMs on the LUN we had to change the snap reserve to 100%. We quickly ran out of space and turned off snapshots for our virtual environment.
When a snapshot is taken on Nutanix, we don’t copy data, nor do we copy the meta-data. The meta-data and data diverge on a need basis; as new writes happen against the active parent snapshot we just track the changes. Changes operate at the byte level which is a far cry from the 16 MB I had to live with in the past.
Due to the above-mentioned life lessons in LUN-based snapshots, I am very happy to show Nutanix customers the benefits of per-VM snapshots and how easy it to restore a file.
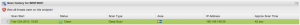
 To restore a file from a VM living on Nutanix you just need to make sure you have a protection domain set up with a proper RPO schedule. For this example, I created a Protection Domain called RPO-High. This is great as you could have 2,000 VMs all on one volume with Nutanix. You just slide over what VMs you want to protect; in this example, I am protecting my FileServer. Note you can have more than one protection domain if you want to assign different RPO to different VMs. Create a new protection domain and add 1 VM or more based on the application grouping.
To restore a file from a VM living on Nutanix you just need to make sure you have a protection domain set up with a proper RPO schedule. For this example, I created a Protection Domain called RPO-High. This is great as you could have 2,000 VMs all on one volume with Nutanix. You just slide over what VMs you want to protect; in this example, I am protecting my FileServer. Note you can have more than one protection domain if you want to assign different RPO to different VMs. Create a new protection domain and add 1 VM or more based on the application grouping.
Latest Security Intelligence Report Shows 24 Percent of PCs are Unprotected
Interesting and scary facts from Microsoft… why not just add a simple cloud based solution like Webroot to your PC’s and Mac’s? Read more about Webroot that I think is a great product here from one of my earlier posts: 1st Test of Webroot SecureAnywhere – #Webroot, #SecureAnywhere, #BYOD
Today, Microsoft released new research as part of its Security Intelligence Report, volume 14, which takes a close look at the importance of running up-to-date antivirus software on your computer. The research showed that, on average, computers without antivirus software are 5.5 times more likely to be infected.
Antivirus software from Microsoft, McAfee, Symantec and others helps to guard against viruses, remove infections and protect your privacy. It can help protect your computer from malware trying to steal your credit card information, e-mail address book or even the files you’ve saved to your computer. It is one of the most crucial defenses computer users have to help protect against cybercriminals.
If you have been using computers as long as I have, long before almost every device was constantly connected to the Internet, you’ll recall the days when viruses were typically spread via sneaker-net, through infected floppy disks. Read more…
Windows #Intune – Toyota rolls out to more than 3000 clients
Automotive Retailer Avoids $1.3 Million in IT Costs with Cloud-Based PC Management Tool
Toyota Motor Europe (TME) had no tools to manage 3,500 car-diagnostic PCs running outside the corporate domain at 3,000 dealerships. TME chose Windows Intune to manage the PCs remotely from a web-based console. It can standardize software deployments to ensure consistent customer service and enhance the security of managed computers to reduce downtime at dealerships. Remote assistance capabilities will also help reduce on-site support costs.
Business Needs
Toyota Motor Europe (TME) manages a network of 30 national marketing and sales companies (NMSC) across Europe. These organizations oversee more than 3,000 dealerships.
In early 2012, TME replaced its stand-alone car-diagnostic tool called IT2 with 3,500 new PCs running more up-to-date software, including Tech Stream and Picoscope. The PCs also store technical documentation. Mechanics attach the PCs to a Vehicle Information Module that connects to a vehicle’s engine to provide critical maintenance information, such as how to reprogram and update a vehicle’s computer chip. The PCs were installed by an external company. The computers are not joined to the domain and operate outside the corporate firewall.
TME did not have a management solution for these 3,500 computers. “We wanted everyone to use the new tools, but we had no visibility into how the dealerships were working with the PCs,” says Niels Svaerke, Manager, Business Process Office, After Sales at Toyota Motor Europe.
NMSC staff downloaded diagnostic software to the PCs from a Toyota intranet site. However, there was no way for headquarters to verify that all dealerships received and installed the software updates concurrently. “It was difficult to ensure that everyone was providing the same level of service by using the same corporate systems and auto diagnostics,” says Dirk Christiaens, Manager of Enterprise Architecture at Toyota Motor Europe. “Also, the head office had no way of knowing if the dealerships deployed an antivirus solution for their PCs, a worrying scenario as they were connected directly to the Internet.”
NMSC employees performed on-site support for mechanics, which often entails travel time. Sometimes, NMSC staff called an external company to reinstall all the software on the PC. Either scenario incurred wasteful downtime at the dealerships.
Solution
To solve these issues, Toyota Motor Europe decided to evaluate Windows Intune, the cloud-based PC management service from Microsoft. Staff at the NMSC can use the web-based Administration console in Windows Intune to run PC management tasks remotely, including software distribution. All that is required is a standard Internet connection, a browser running Microsoft Silverlight, and the Windows Intune client software installed on the PCs at the dealerships. The client returns information on the PC, including software and hardware inventory, and endpoint protection and update status to the Administration console.“We wanted to move into cloud computing, so Windows Intune met our needs perfectly,” says Christiaens. “Windows Intune had a more flexible, pay-as-you-go model, with no additional bandwidth or server costs.”
Read the whole case study here!
//Richard
Five enterprise-ready antivirus systems – #Webroot, @Webroot
This is an interesting article! And I’m happy to see the only cloud-based product on the list!
5: Webroot SecureAnywhere Business – Endpoint Protection
Webroot SecureAnywhere Business – Endpoint Protection is the only solution on this list that is cloud-based only. Some of the others offer a cloud-based service option, but Webroot is the only one that does not offer an on-premise system. However, Webroot is still one of the most impressive applications in the list. The dashboard gives admins a quick overview of their enterprise, endpoint details can be quickly checked, and policies, reports, and logs can be easily viewed. On top of that, though, is the client: it installs in seconds (literally about 6-8 seconds for me) and scans in less than two minutes (1 minute, 42 seconds for my test system). Also, Webroot claims that their client software will run alongside any other security software without conflict. The main disadvantage of this system is its cloud-based nature – company’s deploying Webroot may have limited Internet bandwidth or security concerns with cloud software.

Read the whole article and the other 4 products listed here!
And you can also read my previous blog post about my little review of Webroot here.
//Richard
1st Test of Webroot SecureAnywhere – #Webroot, #SecureAnywhere, #BYOD – via @WeCloud
It’s not very often that I test endpoint protection, antivirus or antimalware software. But tonight I started to have a look at Webroot and I must say that I’m really liking it!
There are some parts in particular that I like about it:
- It’s “cloud” based, so you don’t need your own costly infrastructure!
- It takes seconds to deploy to a new Windows instance
- It scanned the XenDesktop controller that I installed it on in 42 SECONDS! Wow! That’s amazing! 😀
- The footprint is close to NOTHING!
- The installer is just a couple of MB!!
- It fits into the BYOD model
First of I just started a new trial, which was really easy! Just log on to the webpage and register, then after entering your info you’re all set and ready do deploy your “agents”.
My first thought was that this is really great for environments where you’d like low footprint, quick installation and low maintenance efforts of your antivirus software. And the way that Webroot does the scanning of the files etc. is so great and makes the software so quick and neat!
This must be perfect for XenDesktop and XenApp environments is my thought!! I’ll try it our more and will let you know! And why not provide this as an option in your BYOD program?
Here are some reviews that I was given by WeCloud, and they pretty much (or actually more) confirm that this is some good software!
“Easy-to-use and excellently-designed malware protection with powerful central management and deployment features, and which should appeal to a wide range of businesses”.
Read the review here!
AV Wars (RescuTechs LLC)
“No antivirus program we tested performed better at detection and removal of rootkits and scareware.”
Read the review here!
AV Test (Independent IT-Security Institute)
“100% Protection against 0-day malware attacks, inclusive of web and e-mail threats (Real-World Testing)”
Read the review here!









